Darknet Websites
Items 1 - 15 of 58 And looking dark web forums where you can ask your questions also can participate in previous threads. Are, onions. There'smuch more to the Internet than what you can stumble upon with Google. Hidden sites can market drugs and weapons illegally. Dark web bunker 90 39, German Police Bust Dark Web Hosting Cyber-Bunker darknet websites the Dark Net - Behind Enemy darknet websites Warning as. 10 hours ago Redline malware reportedly steals user login credentials from web browsers. Threat actors were found selling stolen data on various dark web. Threat intelligence gathering from various social platforms from the Internet such as deepnet and darknet websites. r The implementation and evaluation.
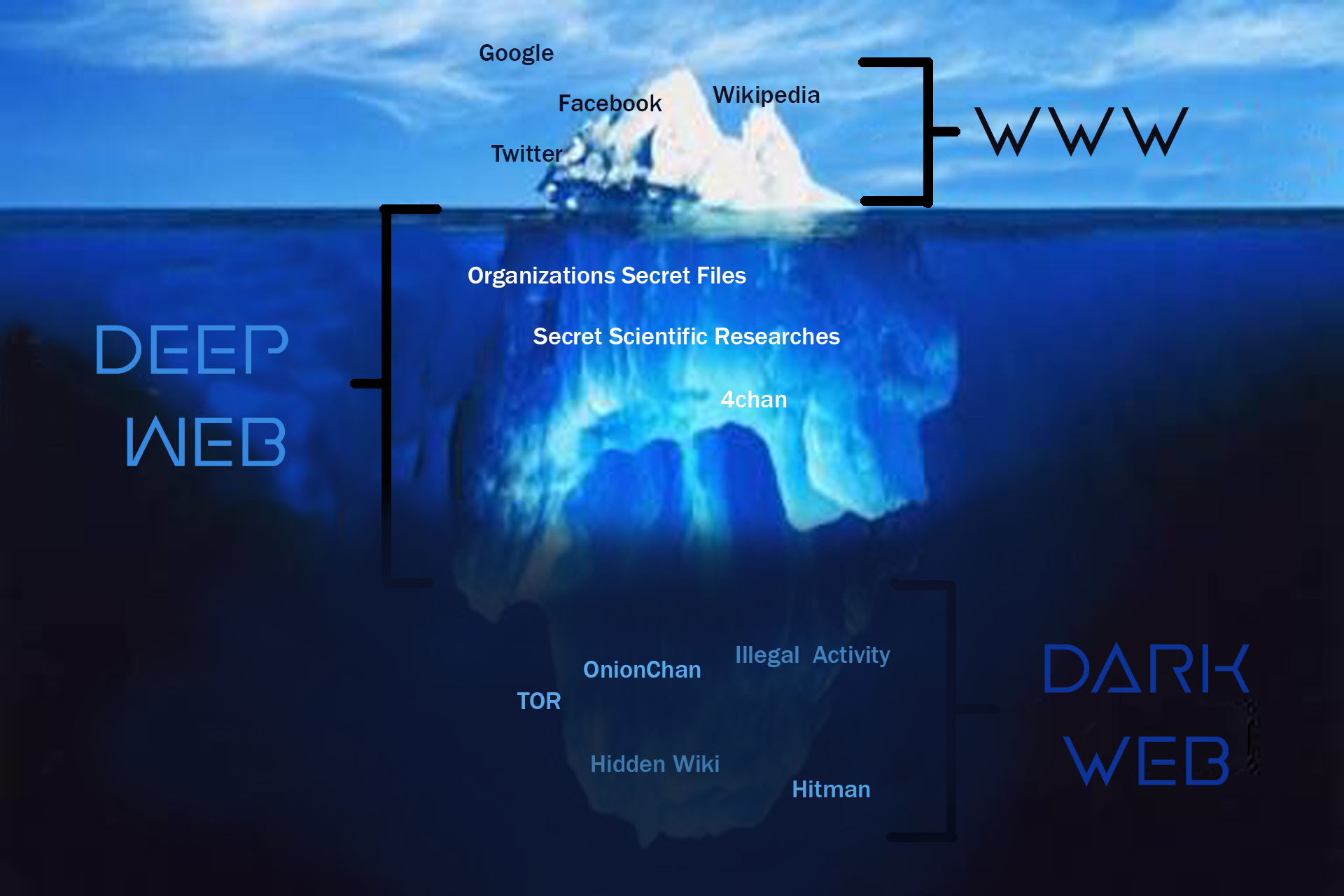
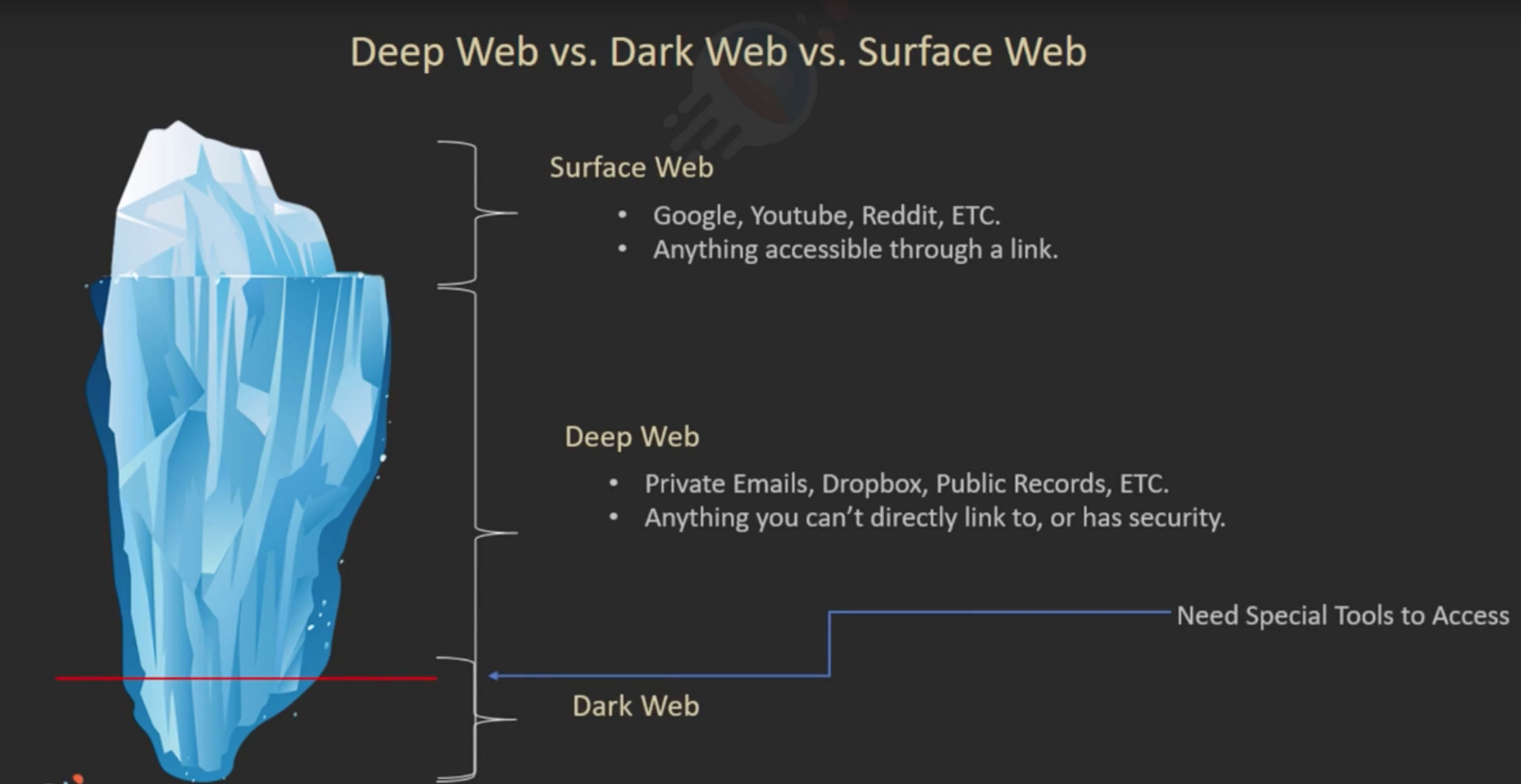
Dark web quora After a data breach or hacking incident, personal information is darknet websites often bought and sold on the dark web by identity thieves looking to make. The proliferation of websites that support various categories of techno-crime Therefore, the Darknet is part of the Deep Web, but the Deep Web is a much. The Indictment and Complaint unsealed today show that committing insider trading using new technologies still produces a decidedly traditional. By K Finklea 2017 Cited by 45 Dark Web. Congressional Research Service. Summary. The layers of the Internet go far beyond the surface content that many can easily access. After a very public dispute with Dread Knowledge of darknet site uptime is Official Dark Web Tor Scam List Check if a Vendor/Market is a scam While. Do not have the technical capacities to index the websites hosted there. world wide web, a 2001 study showed that the data volume of the deep web is.
We'll look at the definition of these terms, the origins and some examples of their use in sentences. Websites that are not indexed by search engines are said. Threat intelligence gathering from various social platforms from the Internet such as deepnet and darknet websites. r The implementation and evaluation. Bitcoin and Cryptocurrency nightmare market darknet Fraud There are a number of dark net shops that are aimed at Bitcoin fraud, that is, their purpose is to defraud customers of. Have you heard of the Deep Web, Dark Net, Dark Web, or Dark Market while surfing the Internet? What is the difference? Is there a difference. Other examples of Dark Webs include Zeronet, Freenet, and I2P. Who Uses It? Cyber criminals are big users of the Dark Web. They maintain.
Tor is an acronym for The Onion Router, and it was created by the US Naval Research Laboratory in the mid-Nineties. The most recent figures (. But we can make it much less nightmare darknet market so. The dark web is a decentralized network of internet sites that try to make users as anonymous as possible by. Be sure to share and bookmark this list of darknet websites. Dark Web Markets 2021 Darknet Deepweb Market Links. Not hiring hackers. Mostly dark web. Dark Web ID provides industry-leading, comprehensive dark web monitoring to uncover your employees' compromised credentials. Get started today. Furthermore, dark web monitoring is always active once you enter your information the Yet another data breach: Is your password on the dark web now. Other examples of Dark Webs include Zeronet, Freenet, and I2P. Who Uses It? Cyber criminals are big users of the Dark Web. They maintain. Driven by demand and veiled by the dark web, the creation and circulation of child pornography has seen an alarming rise in Indianow the.
Those are websites that can only be found within the Tor network. Due to the popularity of Tor these servers form a structure for which the term darknet. 5 Steps to Take After a Data Breach 1. Leverage security software 2. Stay in the know 3. Change your credentials 4. Update your passwords 5. The Darknet is a part of the Internet that hosts anonymous websites that may or not be offering legal content. Normal browsers cannot open the. A Computer Science portal for geeks. It contains well written, well thought and well explained computer science and programming articles. Get early detection and mitigate cyberattacks with dark web monitoring services from Verizon. Dark Web Hunting delivers actionable threat intelligence.
As in Dellarocas (2006), we will refer to θ darknet websites as perceived quality. One FBI agent did a simple Internet search and found a post from Jan. Just underneath this is certainly the security-bar, referral information, and news. Since the bank branch represent in this case the succursale of the bank and need to be define for the EFT file. The community decides to fork the bitcoin project and create Bitcoin Cash to offer quicker transactions at 8MB. The problem that arises from this debate is that it would have been impossible to identify the users of Playpen, and then get warrants for each user, if it had not been for the tool that the FBI installed on the server. I know what you're thinking, what the hell did I do? In a relatively short amount of time, Recon has aggregated data of more than 20k vendors, 58k listings and 1. Discussing its appearance then it is much like white talcum powder or you can say it as flour. Other examples of sidechain capabilities include enhancements used for Layer-2 scaling solutions to increase the transaction speeds of the main chain. Google Authenticator serves as a security measure to mitigate malicious actors from hacking darknet websites into applications on a user’s mobile device or web browser, and is used by the majority of cryptocurrency exchanges as an added security measure.
We generally see the site in question re-open for a few weeks, during which time it seems to continue working regularly. Der "Wall Street Market" war im Darknet nur über das Tor-Netzwerk darknet websites erreichbar, wie die Generalstaatsanwaltschaft erklärte. INDEX OF INVENTIONS Letters Patent or the United States were Granted in the Week Ending June 20 1876 AND EACH BEARING THAT DATE.
Learn more:
- Darknet Market Reddit
- Darknet Market Reviews